New Features and Functionality
Version 8.0 marks a significant milestone in ThreatConnect’s evolution. This release introduces the Agentic Threat Intelligence Platform—a reimagining of what a threat intelligence platform can do for your team. Rather than requiring you to know what to search for, build your own automations, or spend hours assembling reports manually, ThreatConnect 8.0 introduces pre-built AI agents that do the heavy lifting for you: answering questions about your data in plain language, generating threat models with a single prompt, drafting intelligence reports in seconds, and even helping you build well-structured Intelligence Requirements (IRs) through a guided conversation. Alongside these agentic capabilities, 8.0 delivers an improved case management experience; table customization features across the platform; and a cleaner, more transparent set of CAL feature controls—all building toward a faster, more intuitive platform that lets your team spend more time on analysis and less time on everything else.
Agentic AI [BETA]
ThreatConnect 8.0 introduces the platform’s first suite of purpose-built AI agents. These agents are designed to automate defined use cases and give you a natural way to interact with your data—without requiring you to build playbooks, write ThreatConnect Query Language (TQL) queries, or hire technical resources to create automations on your behalf. These agents are built on ThreatConnect’s proven playbook architecture, combining an LLM reasoning layer with direct access to your ThreatConnect intelligence and workflow data.
Version 8.0 includes four agents, which you can easily access by clicking ✨Ask AI at the upper right of the top navigation bar. The agentic AI system processes the question or directive you enter into the Ask AI drawer and determines the agent best equipped to respond to the request.
| Agent | Description |
|---|---|
| ThreatConnect Query Agent | The ThreatConnect Query Agent can access active security investigations and surface relevant threat intelligence to support your defensive workflow, including related Indicators of Compromise (IOCs), similar attack patterns, affected assets, recommended response actions, and contextual threat data. It prioritizes that information by relevance and urgency to enable quick defensive decisions. |
| STRIDE Threat Modeling Agent | The STRIDE Threat Modeling Agent takes the name of a threat actor group or malware family and generates a Threat Model report using the STRIDE framework, which breaks down threats into the following categories: Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege. By using these categories to identify the threat posed by a given threat actor group or malware, cyber defenders can implement security controls to mitigate the threats. |
| Intelligence Report Generator Agent | The Intelligence Report Generator produces tailored threat intelligence reports in three formats: executive, technical analysis, and deep-dive. Each report type is optimized for its target audience, ranging from business-focused summaries with impact assessments for leadership, to IOC-rich technical briefs for SOC and IR teams, to comprehensive deep-dive reports covering threat actor background, attribution, and detection guidance suitable for mixed audiences |
| Intelligence Requirement Creator Agent | The Intelligence Requirement Creator guides you through a conversational, step-by-step process to create Intelligence Requirements (IRs) in ThreatConnect, asking targeted questions and suggesting keywords to help define priorities. Especially valuable for less mature programs, this agent lowers the barrier to entry for the intelligence life cycle by ensuring that you have the right information captured before anything is created. |
ThreatConnect Query Agent
The ThreatConnect Query Agent provides a chat-based interface for asking questions about the data in your ThreatConnect instance and receiving natural-language responses. Rather than navigating to a specific object or building a search query, you can describe what you want to know and let the agent find and summarize the relevant information for you.
- Tell me about the [CYBERSECURITY EVENT] in [MONTH YEAR]
- What do we know about [TOPIC]?
- Tell me about [THREAT INTELLIGENCE OBJECT]
- What’s new since [TIMEFRAME]?
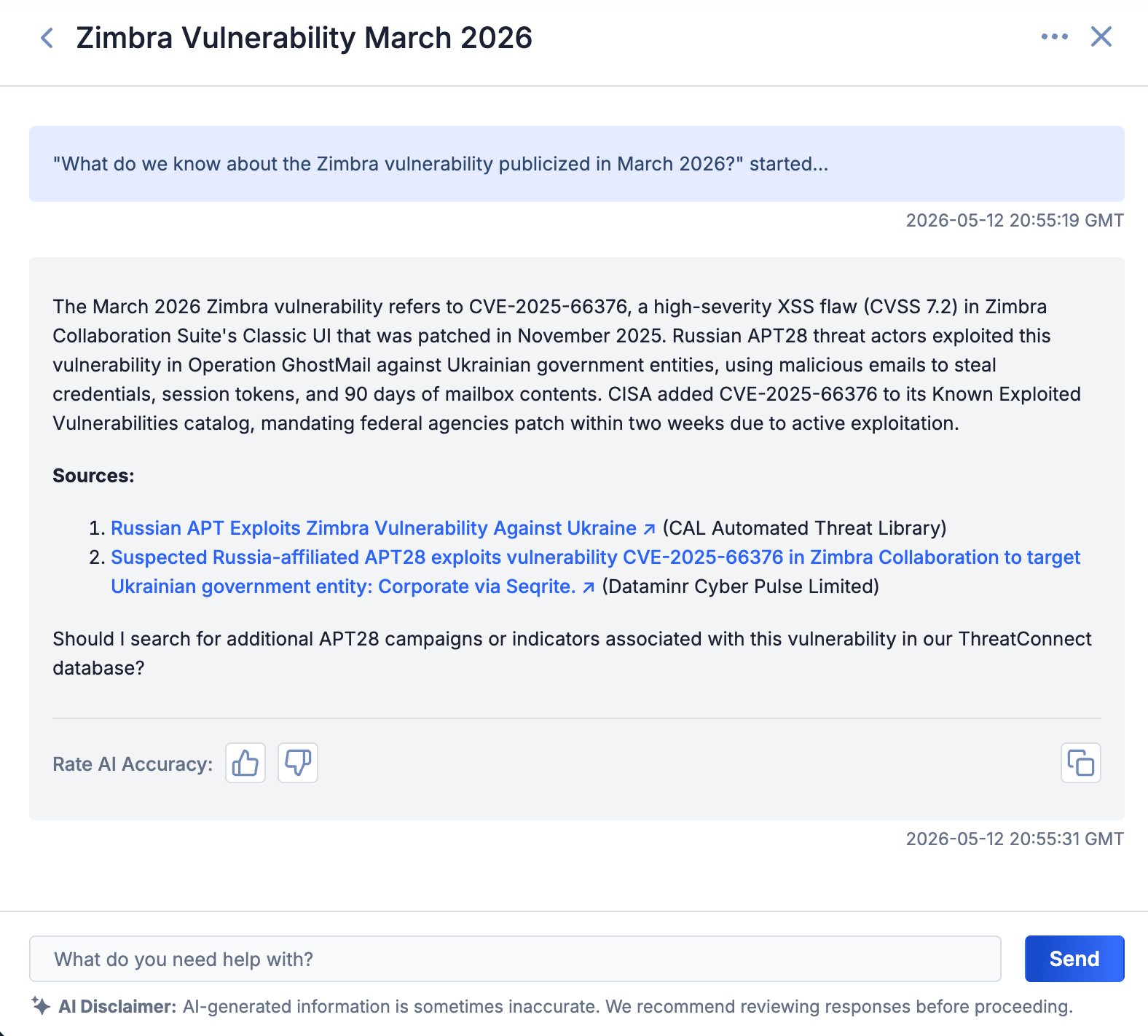
The ThreatConnect Query Agent summarizes your ThreatConnect data on a particular topic
ThreatConnect Query Agent responses include source links so you can easily verify the information and drill deeper when needed. You can also copy responses directly for inclusion in finished intelligence products. After each response, you can rate the accuracy of the agent’s answer to help improve its performance over time.
STRIDE Threat Modeling Agent
The STRIDE Threat Modeling Agent generates structured threat models from a prompt in the Ask AI drawer or via a dedicated ✨ Create STRIDE Threat Modeling Agent Report dropdown on Threat Actor Profiles’ (unified view) Details screens. To use the agent from the Ask AI drawer, ask for a STRIDE report for a named threat actor group or malware family, and the agent will produce a comprehensive threat model that includes relevant MITRE ATT&CK® techniques, mitigation strategies, detection examples, and—in Organizations that have the ATT&CK RQ Financial Impact feature configured in the ATT&CK Visualizer—customized industry firmographics. Options for copying and rating the accuracy of the report are available at the bottom of the response.
- Give me a stride report for [THREAT ACTOR]
- STRIDE report for [MALWARE]
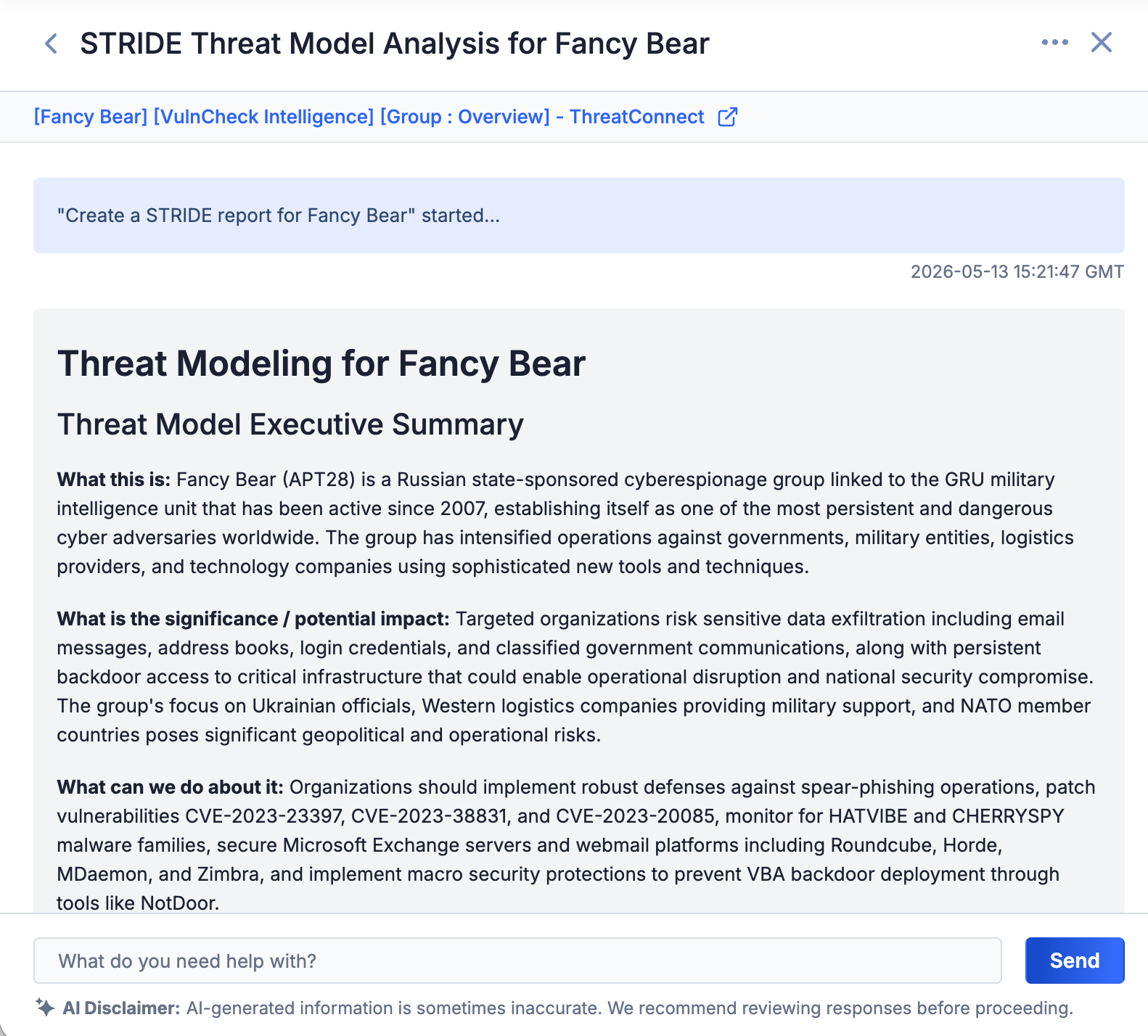
The STRIDE Threat Modeling Agent creates a report directly in the Ask AI drawer
To use the agent from a Threat Actor Profile’s Details screen, click the ✨ Create STRIDE Threat Modeling Agent Report button, and the agent will automatically create and open the report in the ThreatConnect report editor, where you can customize, save, publish, or export it.
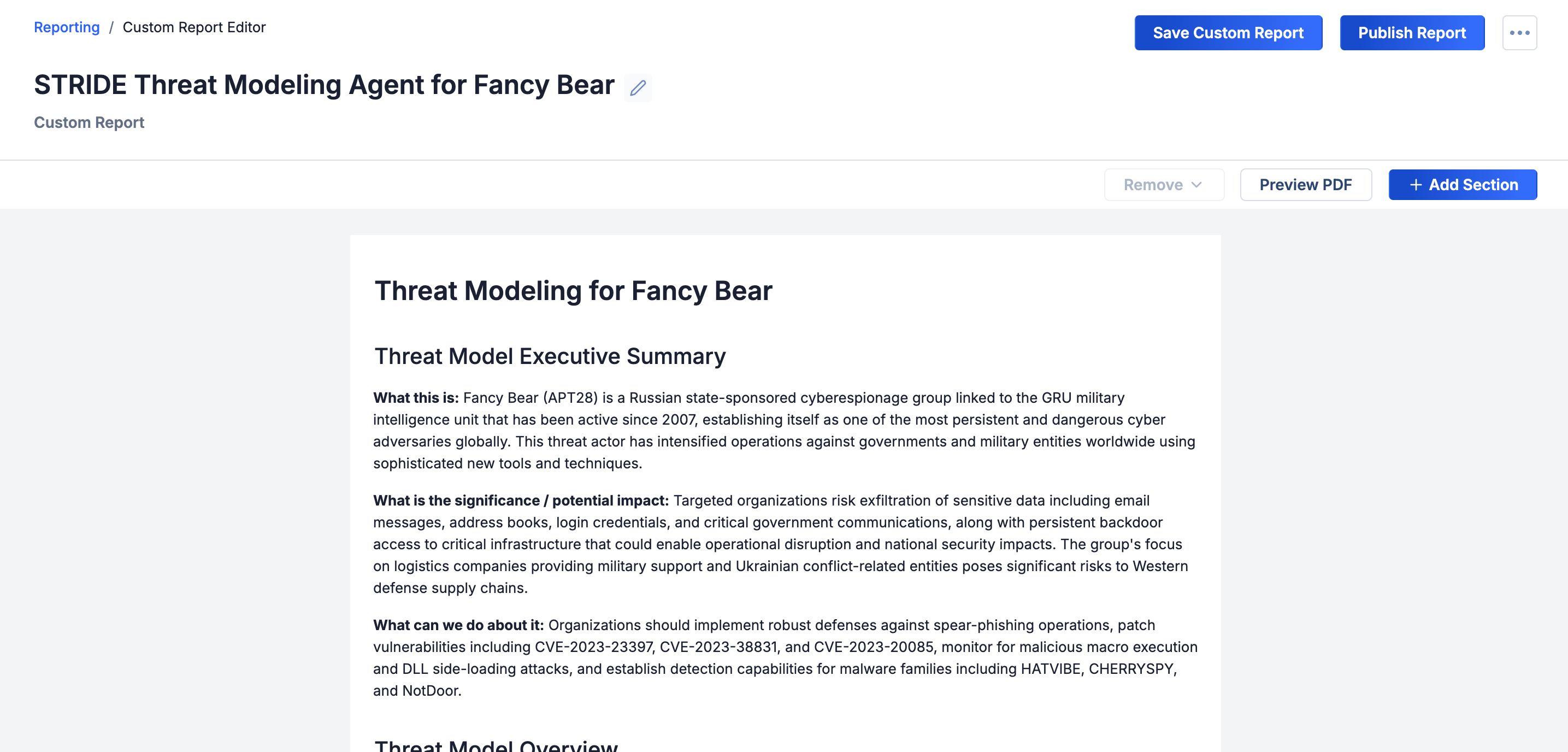
The STRIDE Threat Modeling Agent creates a report in the ThreatConnect report editor
Intelligence Report Generator Agent
The Intelligence Report Generator Agent drafts finished intelligence reports from your ThreatConnect data. You choose the report type and topic, and the agent provides a report with the appropriate format and level of detail for the intended audience: executive-level briefs for leadership, technical analysis reports for SOC and IR teams, and deep-dive, strategic reports for stakeholders who need a holistic understanding of a threat.
- Build a technical-analysis report about [TOPIC]
- Build an executive-level report on activity of [ACTOR] from [DATE RANGE]
- Build a deep-dive report on [TOPIC]
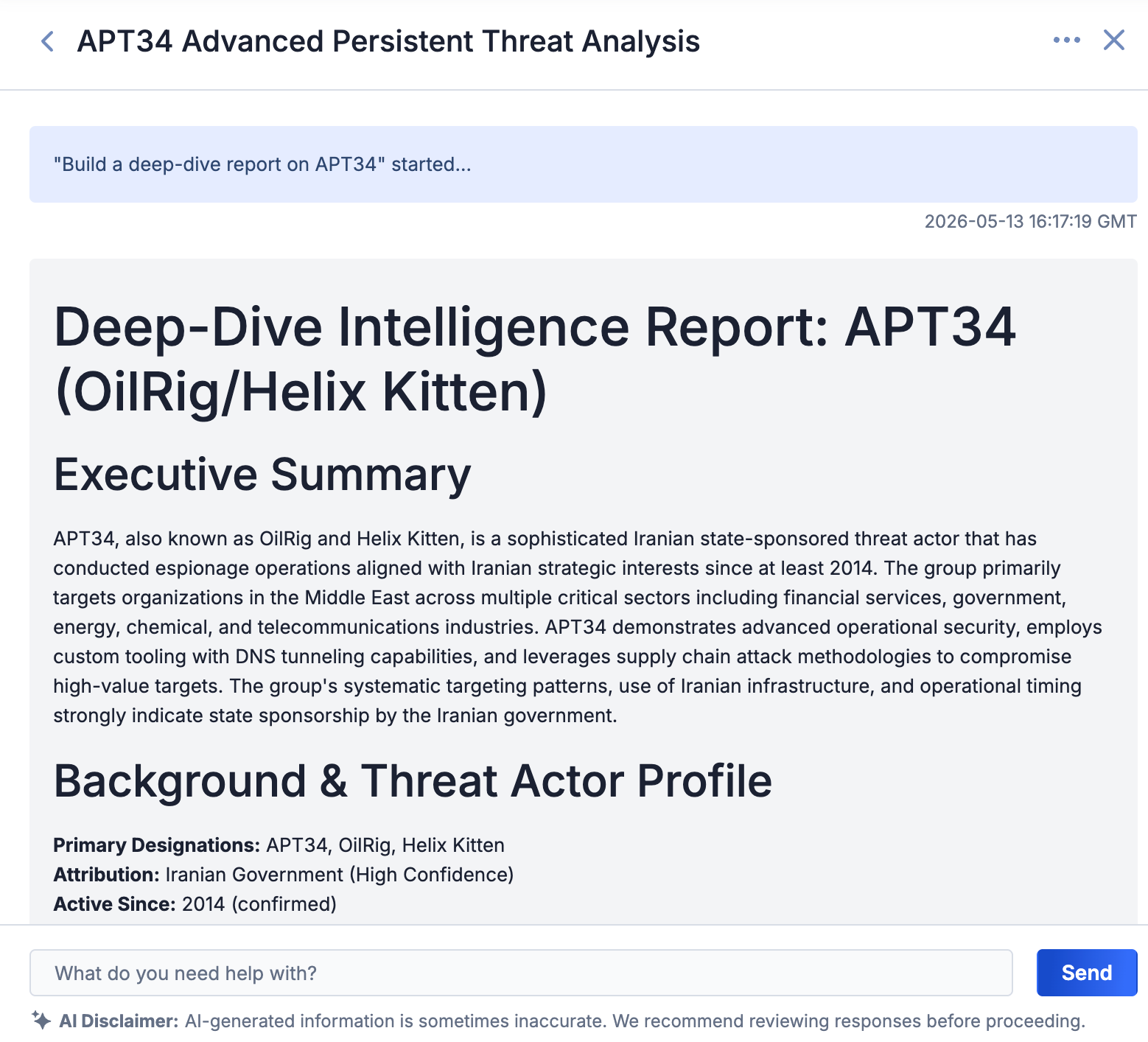
The Intelligence Report Generator Agent creates a fully finished report on a specified topic for your intended audience
Intelligence Requirement Creator Agent
Building well-structured IRs can be challenging. The Intelligence Requirement Creator Agent guides you through the process via a conversational interface: asking clarifying questions, suggesting keywords and metadata, checking for conflicts with existing IRs, and ultimately creating a complete, well-defined, actionable IR on your behalf.
- I need to create an intelligence requirement about [TOPIC]
- Help me create an intelligence requirement for threats to [INDUSTRY]
- Help me create an intelligence requirement for threats to [INDUSTRY] in [LOCATION]
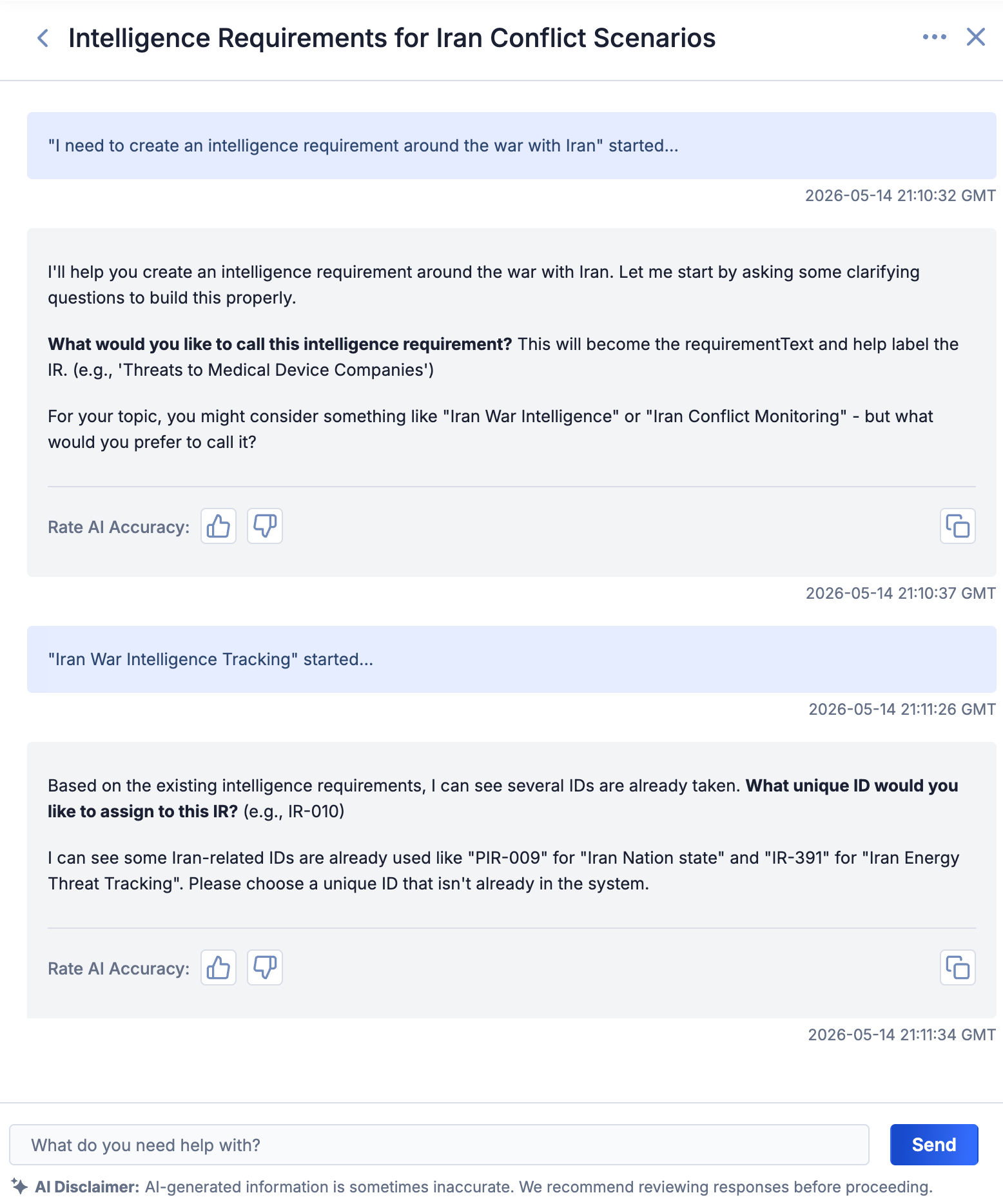
The Intelligence Requirement Creator Agent guides you through creating an IR
Playbooks: Route and Parameter Sets
ThreatConnect 8.0 includes two additions to the playbooks experience that make it easier to build, maintain, and reuse automation logic.
Playbook Routes
The playbook routes feature introduces a switch-statement branching pattern to playbook node connections, eliminating the need to chain multiple If/Else operators when branching on the value of a single output variable. Instead of building a cascade of Boolean conditions to route execution, you can now define named routes directly on an app’s outgoing connections, making the branching logic immediately visible in the canvas.
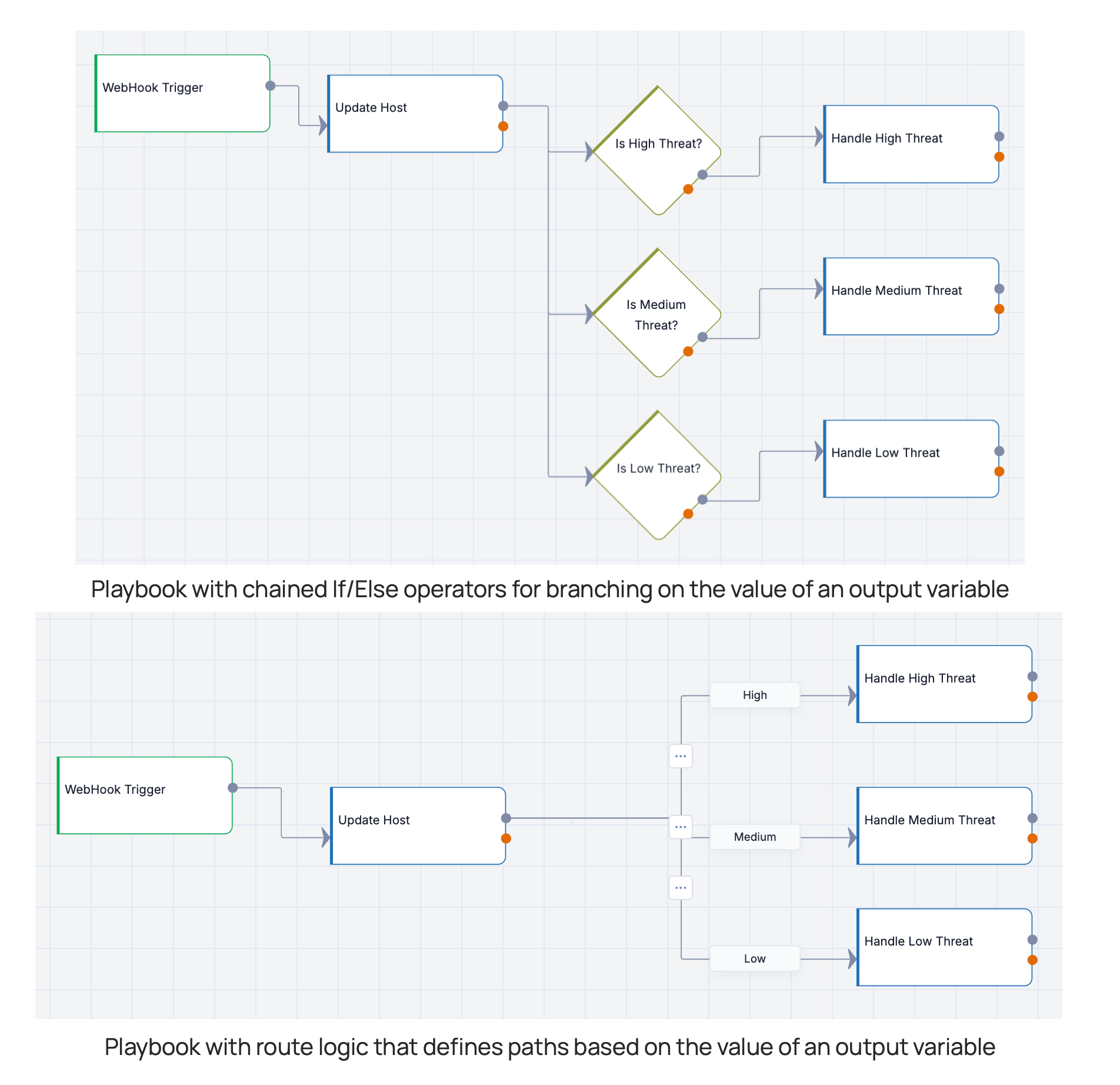
Routes are clearer and more efficient than chained If/Else operators
Routes offer several productivity benefits over chained If/Else operators: They reduce the number of nodes in a playbook; make branch logic visible directly on the connections themselves; and allow you to add, remove, or rename a branch by editing a single route label rather than restructuring a chain of condition nodes.
When defining routes for an app, select the output variable whose value will determine the path of execution. For each value that corresponds to a path, add a route name that matches the value. (Matches are case insensitive, but must otherwise be exact.) Every app with routes also includes a non-removable Default route that handles any output not explicitly named.
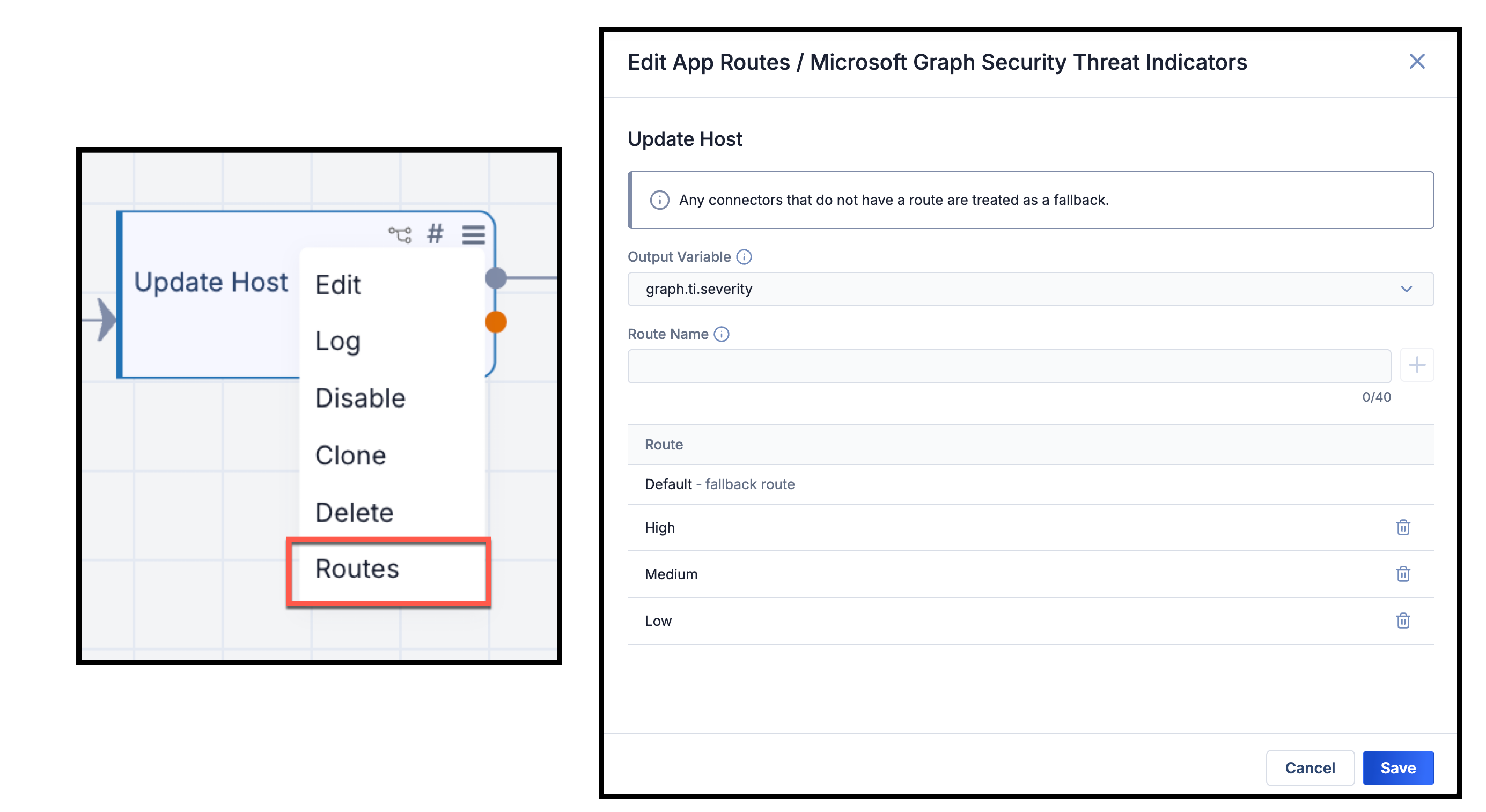
Define routes for app’s downstream execution based on an output variable’s value
Parameter Sets
Parameter sets allow you to create, manage, and reuse collections of pre-configured app parameters across playbooks in your Organization. Rather than configuring the same app settings repeatedly across different playbooks, you configure a single parameter set once and apply it wherever needed.
You can define a parameter set in the Parameter Sets tab of the new Configurations drawer or from the app’s configuration. Once you’ve selected an app, just give the parameter set a name, select the parameters to include in the set, provide the values for those parameters, and save the parameter set. Then, whenever you configure that app in a playbook, select the parameter set to automatically fill in the defined values in the app’s configuration. Saved parameter sets are available for all users who can build playbooks in your Organization.
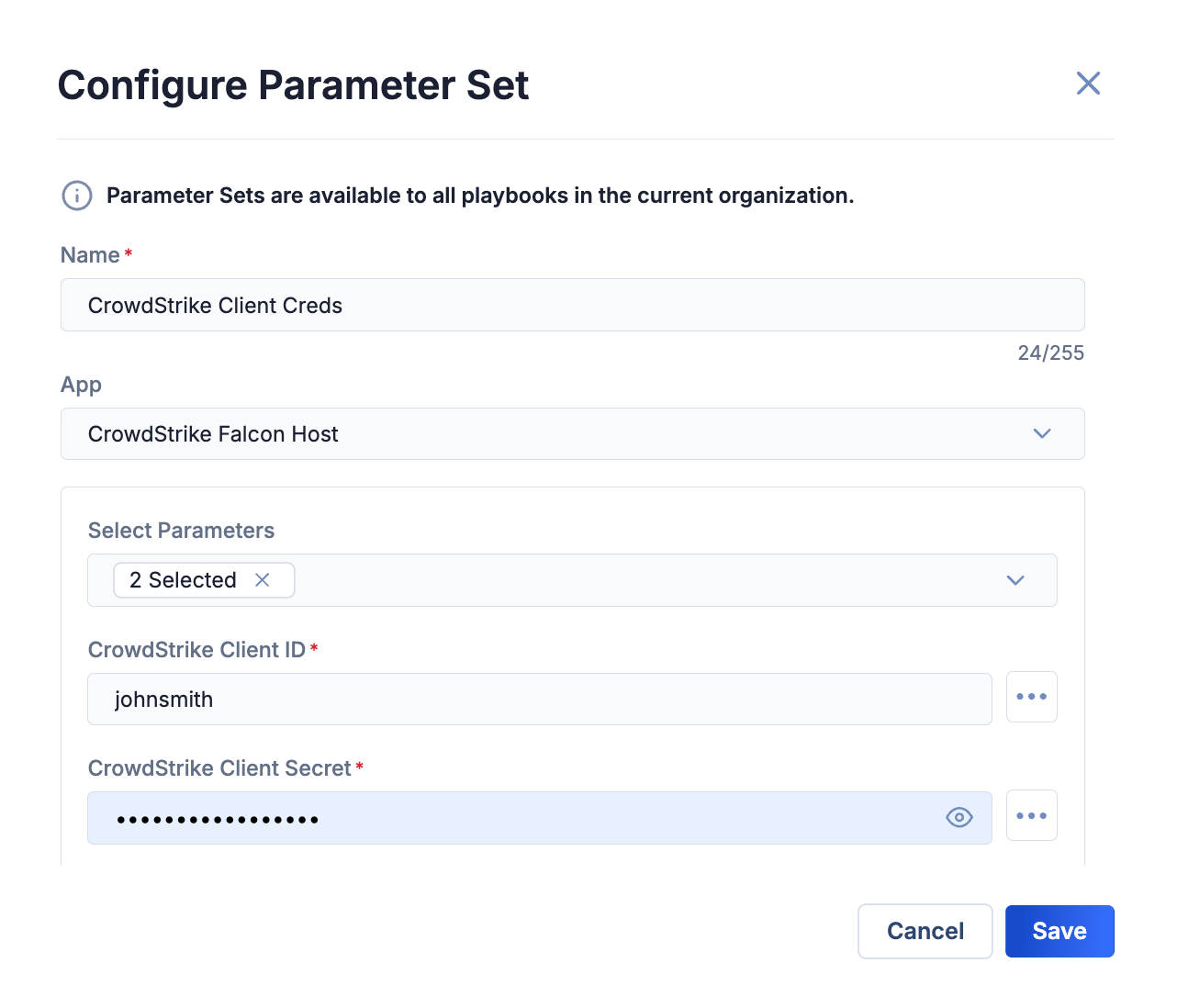
Pre-configure parameters that can be used in an app across playbooks
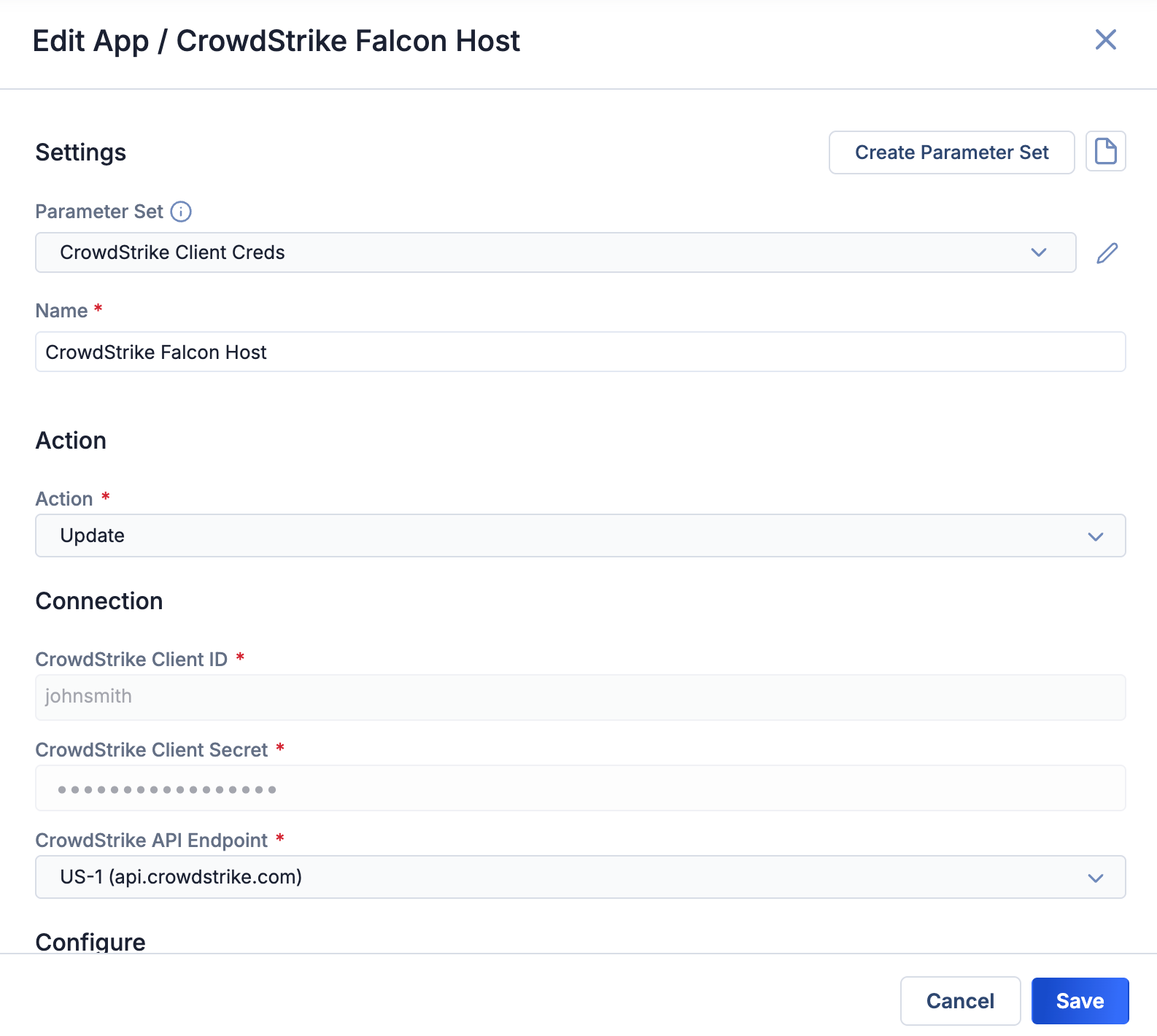
When configuring an app, select a parameter set to autofill its defined values
This feature also includes guardrails that warn you when you attempt to modify a parameter set currently in use by active playbooks, as well as app versioning logic that ensures parameter sets are always created against the latest installed version.
Case Details Screen Improvements
The Case Details screen has been redesigned with the familiar tabular layout from the Indicator, Group, and IR Details screens, reducing visual clutter and providing a more consistent experience. In particular, the timeline and associations cards, which previously occupied space on the crowded main Case Details screen, now have their own dedicated tabs. This reorganization makes it easier to find the information you need while significantly reducing the need to scroll.
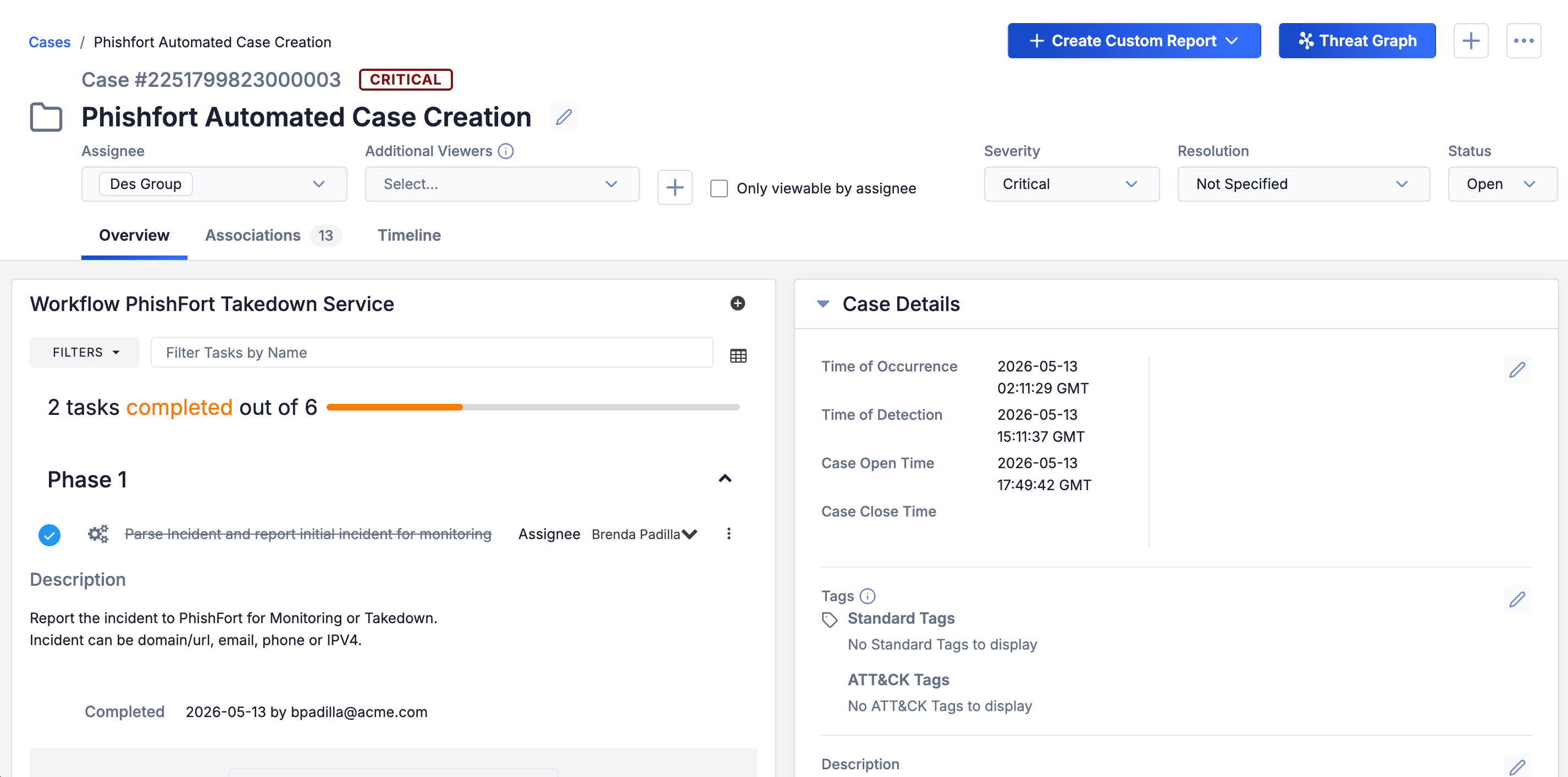
The Case Details screen’s familiar tabbed layout makes it easier to view and find data
Column Reordering and Resizing
ThreatConnect 8.0 gives you control over table layouts across the platform. You can now manually resize columns and reorder them via drag-and-drop in the following areas:
- All Search screens
- All tables on the Associations tab of Indicator, Group, and IR Details screens except the TQL Queries tables
Column configurations—both width and order—persist across sessions, so your layout is preserved the next time you return. You can reset any table to its default configuration at any time.
Defined CAL-Related Feature Flags
Managing CAL-related system settings has historically been confusing; a single CALEnabled setting served as a catch-all switch for fundamentally different capabilities, and some features had no clear way to be disabled independently. ThreatConnect 8.0 replaces this model with two distinct, clearly labeled controls that map to feature areas CAL provides to ThreatConnect.
CALIndicatorEnrichment
The CALEnabled system setting has been renamed as CALIndicatorEnrichment. This is the master switch for global CAL telemetry and Indicator enrichment. When it is enabled, ThreatConnect shares anonymized Indicator telemetry data with CAL in exchange for enrichment data for the Indicators on your instance. When it is disabled, no telemetry is shared and no CAL Indicator enrichment is provided. This setting applies to Indicators only.
CALServices (New)
CAL services are now configurable via a new CALServices system setting with four discrete levels. Each level builds on the previous one—you cannot enable a higher level without its prerequisites. The levels are as follows:
- Disable CAL Services: This level turns off all CAL services. Individually enabled OSINT feeds such as the CAL Automated Threat Library continue to function.
- CAL Context: This level provides read-only access to CAL data with no customer data processing. The provided services at this level are Vulnerability and threat actor data for the Vulnerability and Threat Actor Profile unified view features, respectively, as well as the ATT&CK Tags that power the ATT&CK Visualizer.
- CAL Data Processing: This level includes all CAL Context services and non-AI data processing. It enables the non-AI-powered capabilities of Document Parsing Import and Intelligence Requirement keyword suggestions.
- CAL AI Processing: This level includes all CAL Context and CAL Data Processing services and AI-powered analysis and enrichment services. It enables AI-powered MITRE ATT&CK technique and sub-technique detection in Document Parsing Import.
Turning off the Enable CAL Data permission for an Organization (Account Settings > edit an Organization > Organization Information > Permissions) on a ThreatConnect instance that has CAL Indicator enrichment turned on and the highest level of CAL services (CAL AI Processing) enabled will do the following:
- CAL Indicator enrichment data will not display for users in that home Organization.
- Only the CAL Context services will be provided to users in that home Organization. CAL Data Processing and CAL AI Processing services will not be available to those users.
Unified View Support for On Premises Deployments
Unified views for Vulnerability Groups and Threat Actor Profiles, introduced in ThreatConnect 7.10 and 7.11, respectively, previously required a live connection to CAL to retrieve the baseline data that power these features. As a result, some On Premises instances were unable to take advantage of them.
ThreatConnect 8.0 resolves this problem with two new content packs that deliver the baseline data for Unified Views:
- The Vulnerabilities content pack provides the CAL vulnerability data that power unified views for Vulnerability Groups. Due to the continuous publication of new vulnerability data, updated Vulnerabilities content Packs will be made available at a regular interval going forward.
- The Threat Actor Profiles content pack provides the CAL threat actor data that power Threat Actor Profile features. These data are currently based on the MITRE dataset. As such, the content pack will be updated when MITRE releases updates; at present, this occurs twice each year.
Installation and update of both content packs follow the same process as for existing MITRE ATT&CK content packs. Customers without a live CAL connection should contact their Customer Success representative for instructions on obtaining and installing the new content packs.
Improvements and Bug Fixes - Coming Soon!
Maintenance Releases Changelog
There are no patch releases at this time. 8.0 is the latest version.
ThreatConnect® is a registered trademark, and CAL™ is a trademark, of ThreatConnect, Inc.
MITRE ATT&CK® and ATT&CK® are registered trademarks of The MITRE Corporation.