- 14 Mar 2025
- 2 Minutes to read
-
Print
-
DarkLight
-
PDF
CAL 3.10 Release Notes
- Updated on 14 Mar 2025
- 2 Minutes to read
-
Print
-
DarkLight
-
PDF
New Features
CAL ATL AI Feedback
You can now provide direct feedback about what is working and what needs improvements in the AI summaries for CAL™ Automated Threat Library (ATL) Reports! Use the new Rate AI Accuracy feature on the AI Insights card to let us know if you find the summaries to be helpful, if they have problems, or if you have specific ideas about how they could be improved. The feedback is anonymously collected and used to create improvements to future AI summaries in ATL.
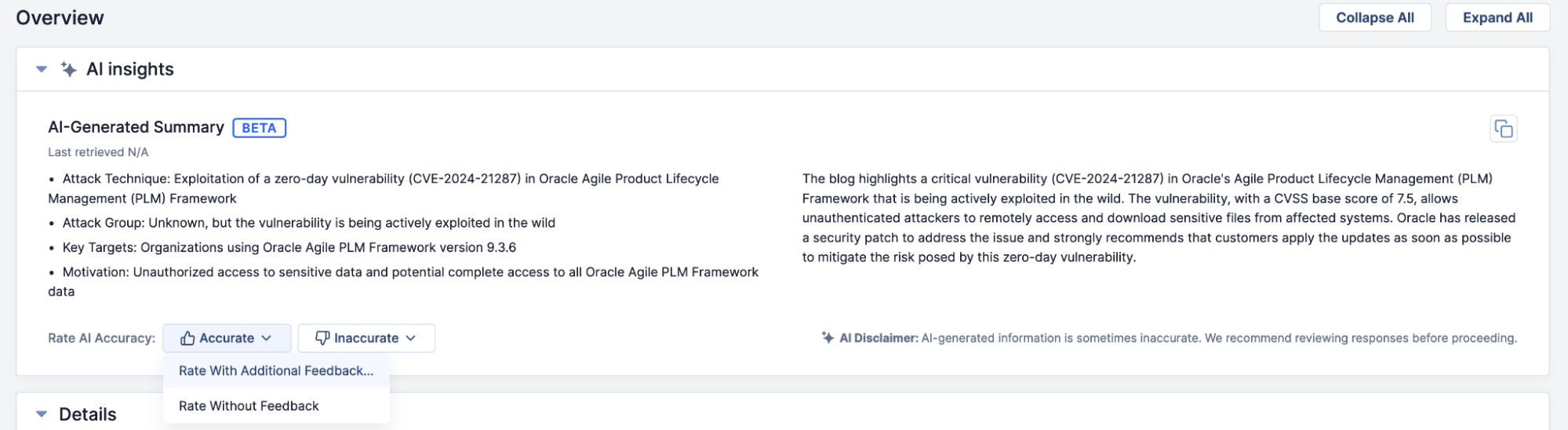
Provide feedback on AI summaries for CAL ATL Reports directly from the Details screen
Updated Features
Hourly CAL ATL Updates
The CAL Automated Threat Library now delivers fresh insights more frequently throughout the day, empowering you with up-to-date information from trusted open-source intelligence providers. Access Indicators, MITRE ATT&CK® mappings, AI-powered summaries, industry insights, and more—faster than ever before.
- Timely intelligence: 33 blogs are now updated hourly for quicker access to critical insights.
- Enhanced coverage: Five additional sources will be updated multiple times daily for even greater visibility.
- Continuous improvements: More sources are under evaluation, so expect more updates to more sources more often…soon!
For Dedicated Cloud customers, the CAL Automated Threat Library v1 Job App was updated to deliver hourly updates starting on January 8, 2025. For customers with On-Premises instances, the update is delivered automatically with the ThreatConnect® 7.8.1 release. Please feel free to reach out to your Customer Success Manager with questions about this feature.
MITRE ATT&CK 16.0
ThreatConnect version 7.8 includes an update to MITRE ATT&CK 16.0, which adds 19 new techniques and sub-techniques, 33 new types of software, 11 new groups, 6 new campaigns, and 1 new course of action.
All MITRE ATT&CK framework items (techniques, software, groups, campaigns, course of action) can be visualized when modeling and exploring relationships in ATT&CK Visualizer and Threat Graph (i.e., when pivoting with CAL) and can be directly identified in textual content when using ThreatConnect Intelligence Anywhere, the Doc Analysis Import feature, and the Doc Analysis Playbook App. They can also be leveraged from the Browse screen, ThreatConnect’s search engine, and in Intelligence Requirements.
Improvements
- Improvements were made to the ordering of results for Intelligence Requirements Global preview and daily results to provide more valuable matches to keywords.
- The CAL Safelist was expanded to include more trusted domains. With this update, CAL protects you from the distraction of an additional 1600+ Indicators in the ThreatConnect platform as well as makes this information clear in the ThreatConnect CAL integration with Polarity. CAL is working to constantly improve the accuracy of your threat intelligence, allowing you to focus on real threats while providing contextual insights and minimizing unnecessary noise in analyst research, document analysis, Indicator queries, and automated workflows across both ThreatConnect and Polarity.
ThreatConnect® is a registered trademark, and CAL™ is a trademark, of ThreatConnect, Inc.
MITRE ATT&CK® and ATT&CK® are registered trademarks of The MITRE Corporation.


