Overview
Email ingestion in ThreatConnect® is a valuable part of the threat intelligence workflow process. Storing the information that an email holds, such as potential IOCs or tracking on phishing campaigns, allows for better response based on the data collected. This article describes important configurations and settings for email ingestion in ThreatConnect.
Before You Start
| Minimum Role(s) | System role of Administrator to change email domain and delivery custom settings |
|---|---|
| Prerequisites | None |
Push Emails to ThreatConnect
The core actions inside ThreatConnect require that emails be delivered to the ThreatConnect server from a mail server rather than having ThreatConnect pull them. Therefore, the setup for the mail server must have configurations added to the mail routing to ensure that the emails destined for ThreatConnect are delivered. The specific configurations will vary based on the mail server's location(s), the ThreatConnect settings and configurations, and other items such as the email domain used by ThreatConnect.
Email Domain Custom Setting
ThreatConnect has the inbound email domain set to localhost by default. Depending on the mail routing rules, this setting will need to be adjusted to reflect the email domain that the mail servers will use to route the ThreatConnect server's emails. The email domain can be a subdomain of the currently used domain to keep the overhead needed to a minimum by routing all emails for a single subdomain to ThreatConnect, versus setting up mail routing rules for each email address for ThreatConnect.
To change the inbound email domain setting, log in with a System Administrator account, navigate to the Settings tab of the System Settings screen, select the System tab on the left side of the screen, and scroll down to the Inbound Mail section (Figure 1).
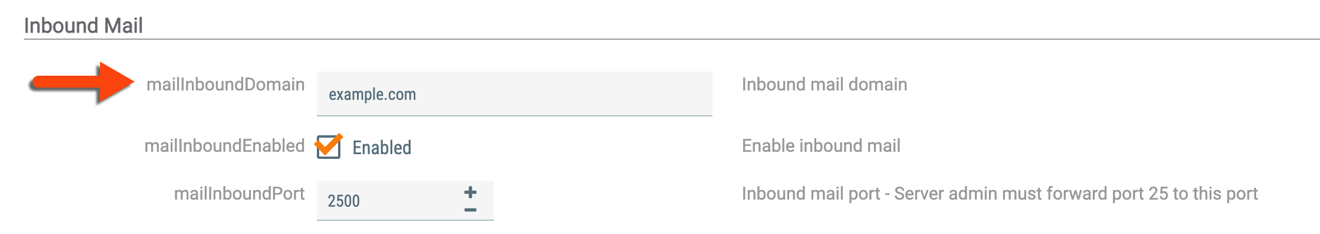
Change the mailInboundDomain setting to the desired subdomain.
Email Delivery Custom Setting
ThreatConnect accepts incoming emails on port 2500 by default. The port forwarding rules described in the “Port Forwarding” section of ThreatConnect Installation Guide_Linux® Operating System allow the operating system to receive the messages on port 25 and then redirect them to port 2500. The port at which ThreatConnect will accept emails can be changed from port 2500 to a custom port.
To change the port, log in with a System Administrator account, navigate to the Settings tab of the System Settings screen, select the System tab on the left side of the screen, and scroll down to the Inbound Mail section (Figure 2).
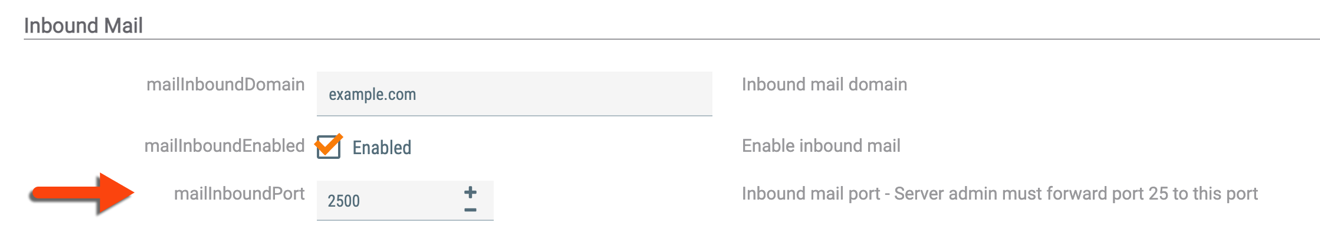
Change the mailInboundPort setting to the desired port.
Storing Emails
Recipient “email addresses” can be created in ThreatConnect via the Feed Mailbox or Phishing Mailbox or by using the Mailbox Trigger in Playbooks. However, these email addresses are not actual mailboxes in ThreatConnect. Rather, they are a routing option for the automation processes that receive the messages. If an automation is not active, all emails destined for the associated email address will be dropped, with no way to reacquire the missed emails.
Any email delivered to ThreatConnect that does not have a matching recipient email address will automatically have its message dropped. If a message has a matching recipient email address, it will send the message to that automation. The automation will not retain the message in its entirety, but will break it into parts. The Playbooks Mailbox Trigger will provide all the available message parts to be stored as an Email Group object, which is the closest option for retaining the message as a whole. To store copies of email messages in their entirety, set the mail routing configuration to forward a copy of the email message to another mailbox for the record.
ThreatConnect® is a registered trademark of ThreatConnect, Inc.
Linux® is a registered trademark of Linus Torvalds.
20106-01 v.01.B